Author: Kent Moors, Ph.D.
Before moving into this week’s edition of the Classified Intelligence Brief Spy Tale series, the usual background involves a stroll into the operational distinctions that determined what I did in “government service.”
At least what I did most of the time in those episodes that “mother” allows me to write about (I note once again here that negotiations remain ongoing).
Producing intelligence while protecting the process and making sausage have something in common. One uses what comes out of both, but often would rather not see how either is made.
Over decades of service, my primary function was foreign counterintelligence – watching the other guys someplace outside the U.S.; insulating our ops from their actions; messing with what they were doing; protecting sources and methods, occasionally in hostile environments; and providing the CI component of intelligence reports coming from the field.
The intel community has several manuals of conduct (yes, these do exist). An officer is expected to abide by what is said therein. And you do comply in virtually all cases. However, in an active mission, one would occasionally consider manual dictates and implications before having to evade them in practice. Fortunately, there is a catch all “escape clause” that provides some leverage.
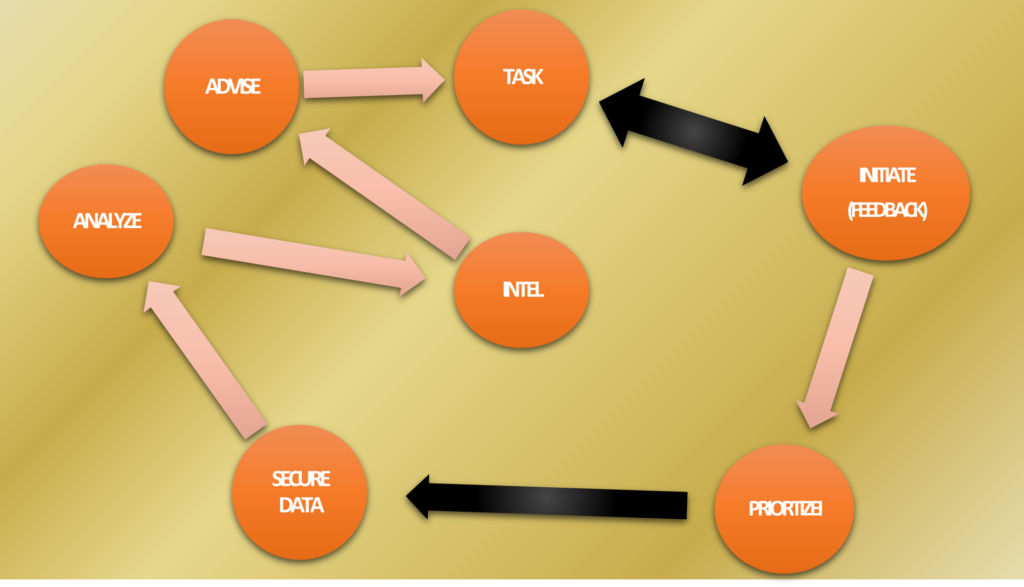
At the base of what I was doing, the manual approach made a separation between CI and foreign intelligence gathering in the field (FI) that is impossible to maintain in practice.
FI is considered the collection of what others tell you (i.e., HUMINT, human intelligence), combined with on the ground communication (COMINT) and signal (SIGINT) intercepts, along with an occasional dash of intel gathered from more open sources (OSINT).
CI, on the other hand, has a dual function according to the National Intelligence Priorities Framework (NIPF). I am taking the following from the 2006 edition, the last for which CI parameters were declassified for public use (the last classified version that included CI particulars was issued in 2015):
CI is composed of both offensive and defensive elements. Offensive CI includes the penetration and deception of adversary groups. Defensive CI involves protecting vital U.S. national security related information from being obtained or manipulated by an adversary’s intelligence organizations, activities and operations. This two-pronged approach forms a comprehensive CI strategy that is informed by collection results and feeds more effective CI operations. Counterintelligence is a universal constant that should be factored in whenever U.S. intelligence or national security capabilities are deployed or when we are targeted by our adversaries. ‘Every’ U.S. intelligence capability and requirement needs to be protected and ‘every’ intelligence threat
deployed against us should be countered by effective offensive and defensive CI.
If this explanation is not expansive enough, CI measures and countermeasures are further separated into five functions: operations; investigations; collection; analysis and production; and functional services. This last category is a vacuum cleaner-like domicile for just about anything considered relevant to an operation but not provided for in straight black and white.
Now the primary function of the intel business is to provide usable advice to policy makers. That function is specified in the National Securities Act of 1947, as interpreted later by Executive Orders (EOs), National Security Presidential Directives (NSPDs), and Intelligence Community Directives (ICDs).
An EO or NSPD is issued by the President, the most important for current intel activity being Ronald Reagan’s EO 12333 (December 4, 1981; available via the National Archives at https://www.archives.gov/federal-register/codification/executive-order/12333.html).
An ICD comes from the Director of National Intelligence (or by the Director of the CIA – as Director of Central Intelligence or DCI – prior to the DNI coming on board in April of 2005).
The most complete description of what I did is contained in ICD 750: Counterintelligence Programs, issued by DNI James Clapper on July 5, 2013. The public unclassified version of ICD 750 can be found at: https://www.dni.gov/files/documents ICD/ICD750.pdf
There was no explicit mention of paramilitary or other active measures in the original 1947 legislation but ample opportunity there to graft such activities onto the intelligence mission subsequently. The use of NSPDs to expand “boots on the ground” as an element in the national intelligence mission expanded significantly after 9/11, especially with George W. Bush’s NSPD-26 issued on February 24, 2003.
But the overarching justification for the US organizational apparatus remains the gathering and dissemination of intelligence. All the rest, while present here and there, is largely fodder for novels and Hollywood.
I never once toppled a government, blew up a bridge, or put a virus in anybody’s computer. Regrettably, I also never drove an Austin Martin through the Alps or played baccarat at the Casino de Monte-Carlo.
FYI, and as an aside, baccarat is 100 percent luck. The only enticement comes from the high stakes betting and the narrow margin the house has in either direction. But it never figured in any of my operations (the expense vouchers or operational accountants back home were never that understanding).
Usually, what I did was colored by a fair amount of routine and boring repetition. Yet it was upon occasion anything but ordinary. There are a lot of anecdotal examples but no textbook on doing good intel. In training, I once asked a legendary field operative what made good intel. He answered, tongue in check, “Good intel is what good intel officers produce.”
That figures. My simplistic question sort of set me up for it.
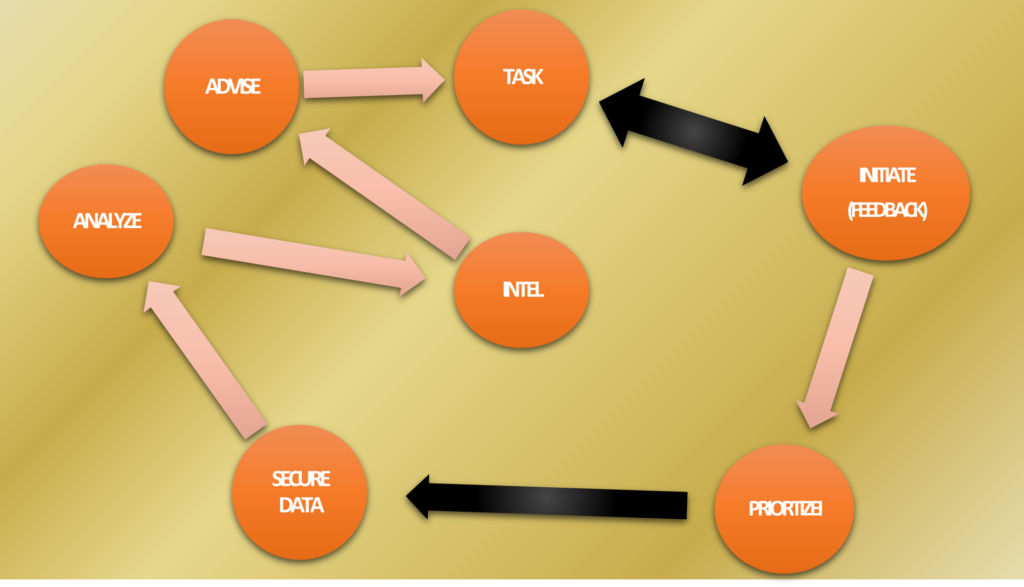
This is not an art; it is a process. It involves data collection and filtering of what is obtained following an instruction (a “tasking”) from a higher pay grade and (after controversies arising in previous scandals) under legislation requiring that it ultimately arises from designated public officials.
Following revisions in procedures, a field officer has the right (and usually the obligation) to ignore a request that cannot document it comes from the requisite authority. The intel world, like the art world, has its own form of a provenance.
The process itself is designed to answer three essential questions: (1) what something is (definition); (2) what it means (analysis); and (3) how use it (intelligence). The third state is the most important. The best advice written in a way that cannot be used, is worthless.
When lecturing at the U.S. Army War College years later, I expressed the process this way:
Unless the report can be applied to an ongoing policy (or in the case of the military, tactical) question, it has largely been a waste of time and effort.
And you cannot waste either of these in the field.
It is against this backdrop that I would apply my responsibilities when called upon. Usually, the requirements of my participation would cut across so-called disciplinary “boundaries” as presented in the manuals. When operational, these documents were not worth the paper they were printed upon.
Still, providing intel advisories is usually not a direct line, nor without its own brand of political kabuki theater. The best estimates are hardly dispositive. They also can be the result of a very messy give and take.
Ninety years ago, the controversial New York Times reporter Walter Duranty was the first to say that “You can’t make an omelet without breaking eggs.” It seems we ate a lot of omelets in my career while trying to avoid the shells.
Under some rather intense pressures to perform in less than optimum situations, mistakes result. I made my share of them. Occasionally, I hung other people out to dry. Take the following Spy Tale as a case in point.
It was 2014 and I was meeting with some regional energy players and officials outside Quito, the capital of Ecuador. This is one of the few entire cities named a UNESCO World Cultural Heritage Site (Krakow in Poland is another and just happens to be the location for an upcoming Spy Tale).


Quito received its UNESCO designation owing to its remarkably preserved old city center, much dating back five hundred years or more. Being there is like traveling back in time. Nestled by the South American Andes mountain range and close by tributary headwaters cascading into the Amazon, this is a beautiful place.
But by 2014 it had suffered from the global economic crisis in large measure prompted by an American credit collapse (subprime mortgages and the derivative paper based on them). That, in turn, had destroyed the value of dollar-denominated assets worldwide. This hit Ecuador hard since it had discarded a domestic currency and adopted the U.S. dollar a decade earlier.
While the “invitation only” meeting for foreign and local energy reps working in Ecuador had been called by a local think tank and they arranged the facilities, the list of invitees had been drawn up (hastily) by us (i.e., me).
My hosts had selected a private location for the six and a half days of meetings – the Hacienda Rumiloma, a quaint boutique mountain hotel overlooking Quito. We apparently took all available rooms for an entire week.
This was to be a genuine meeting to address an actual major intersection of energy and policy. But I had to drain all attending for material related to a tasking I will mention in just a moment.




As was my new normal, it made no difference what my overt reason was for being some place. The “other job” was there as well.
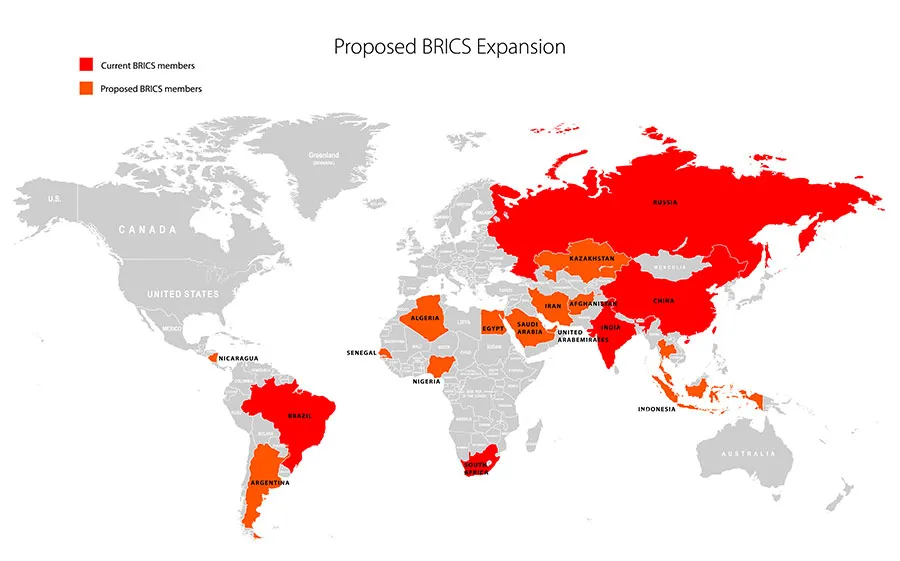
In this case, my meeting involved a rising crisis in Ecuador, Peru, and spreading into Brazil and Argentina where debt owed by both central governments and primary state oil companies was taking on a geopolitical dimension.
The rationale for meeting in Quito resulted from the Ecuadorian crisis being the most advanced. Populist President Rafael Correa’s government and state oil company Petroecuador had run up huge debts to China, and, to a lesser extent, Russia, in a desperate attempt to balance the books.
Didn’t work. For the first time in its history, China had decided to use debt as an instrument to control the foreign production of crude. But this time it was not going to force the oil back to a thirsty Chinese domestic market. This time, Beijing allowed Ecuadorian production to be exported anywhere. Instead, the Chinese were controlling another’s nations oil revenues.
Ecuador was then, and is today, the smallest producing member of OPEC. By 2014, therefore, China had effective control over the oil proceeds of an OPEC member. This was quickly followed by a Chinese national oil refining company, with no experience in the running of crude oil fields, suddenly granted production licenses in one of the most ecologically sensitive basins in the country.
I knew some of the folks thrust into running the operation since I had advised the Chinese company in question on international market matters and previously had two of their rising junior administrative officers as graduate students back home in the US (there is an entirely different story here which I may someday address). On an earlier 2014 visit, I went upriver to visit the Chinese sites.


Of great concern to environmentalists were the Chinese field developments abutting the Yasuni National Ecological Park. These are (or were) pristine Amazonian basin rainforests. Servicing Chinese debt had obliged the government to allow drilling in some of the most sensitive areas in all of Ecuador.


All of this had certainly attracted the attention of Washington. The interest intensified when two other matters emerged.
First, the Chinese pattern of providing credit followed by increasing control over oil revenues was being repeated in Peru, while governments in Brasilia and Buenos Aires looked like they were interested. Second, Moscow was moving to replicate the model for its own use.
From on high came the demand for an expedited report requiring that a multi-agency task force (called a restricted interagency group, or RIG) squeeze every asset they had and lean on others who may or may not have relevant info. There was never enough time to respond to a tasking like this. But this one was even more time sensitive than usual.
Much of the required report dealt with other matters impacting on US Western Hemisphere policy and most of it was conducted in other South American locations. But the energy component was certainly a seminal factor. And that was my bailiwick.
I had earlier advised the largest Petroecuador oil refinery on market ramifications from applying environmental standards to its operations. This is the huge Esmeraldas Refinery, opened to process Amazonian oil. The refinery had operated for years with low environmental standards (and that is being generous). It was a typical practice there to dump its waste effluents directly into the river adjacent to the refinery, while the Trans-Ecuadorian Pipeline from Amazonian fields to the main coastal port of Esmeraldas was a horrific polluter.


By the time I became involved, the Correa government had warmed to the environmentalist position, assisted in no small measure by major opposition from indigenous populations in places like Yasuni and its environs (assisted by foreign media and interest groups) and the ongoing legal battle with American oil giant Chevron over a nasty example of internal pollution. For its part, Chevron claimed it was not the cause. Rather, it blamed its local partner Petroecuador.
Advancing environmental standards would allow U.S. companies to move in and provide services (since they had the experience in retrofitting facilities to meet the standards and could provide some cover for staff to provide “other functions” of interest to policy makers back home).
But there was another reason I was given a higher-than-expected visibility in the RIG. The op had a distinct CI element. It was assumed (quite correctly as it turned out) that Chinese and Russian intel officers had responsibilities in their respective national initiatives involving Ecuadorian (and other South American) energy debt.
I supposedly knew something about CI as well. Which meant this assignment was certain to mix boundaries between “manual specific” responsibilities before it was done.
Our 14-member meeting at Hacienda Rumiloma included seven Ecuadorian guys (both government and company) along with seven foreign reps: two from the Chinese company involved in upstream operations; two from other Chinese interests in Ecuador; two Russians from the recently established Quito branch of a Caracas-based energy investment bank set up by Russian, Venezuelan, and Iranian energy companies; and an American (me).
I had no time to finesse. Everything I encountered having any apparent use was funneled to the agency’s in-country station at the U.S. Embassy down the hill in Quito.


By the second day. I was centering my attention on one of the Russians, a young fellow I will call Gregor, who was certainly low-level SVR (successor to the KGB’s First Chief Directorate in charge of foreign intel), recently arrived in the country, not particularly at ease with the situation, and whose English was only slightly better than my Russian. He early and often revealed material he should not have.
I had to play hardball here; there was no time to be nice about it. Gregor’s largesse figured prominently in my communications to station and I pumped him as much as I could.
Gregor never made it to the end of our meetings. He was pulled out on day six. Before departing, he made a point of finding me and was angry when he did. “You really are a bastard,” he blurted. “No, I am an intelligence officer,” I responded “It is a fine line between the two, but there is a difference. And unless you can find it, you won’t survive in this business very long.”
Maybe the only career advice I ever gave to somebody from the other side.


This is an installment of Classified Intelligence Brief, your guide to what’s really happening behind the headlines… and how to profit from it. Dr. Kent Moors served the United States for 30 years as one of the most highly decorated intelligence operatives alive today (including THREE Presidential commendations).
After moving through the inner circles of royalty, oligarchs, billionaires, and the uber-rich, he discovered some of the most important secrets regarding finance, geo-politics, and business. As a result, he built one of the most impressive rolodexes in the world. His insights and network of contacts took him from a Vietnam veteran to becoming one of the globe’s most sought after consultants, with clients including six of the largest energy companies and the United States government.
Now, Dr. Moors is sharing his proprietary research every week… knowledge filtered through his decades as an internationally recognized professor and scholar, intelligence operative, business consultant, investor, and geo-political “troubleshooter.” This publication is designed to give you an insider’s view of what is really happening on the geo-political stage.
You can sign up for FREE to Classified Intelligence Brief and begin receiving insights from Dr. Moors and his team immediately.
Just click here – https://classifiedintelligencebrief.com/